Hackers hitting thousands of organizations worldwide in a massive phishing campaign forgot to protect their loot and let Google the stolen passwords for public searches.
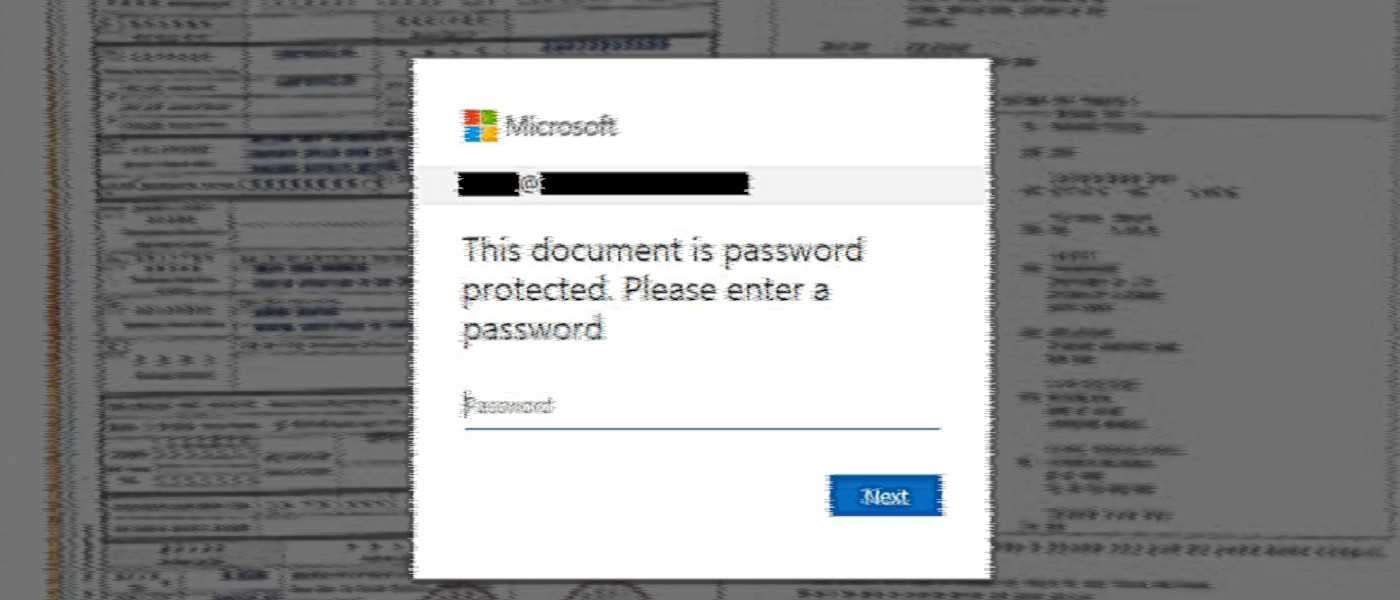
The phishing campaign has been running for more than half a year and uses dozens of domains that host the phishing pages. It received constant updates to make the fraudulent Microsoft Office 365 login requests look more realistic.
Creds in plain sight
Despite relying on simple techniques, the campaign has been successful in bypassing email protection filters and collected at least 1,000 login credentials for corporate Office 365 accounts.
Researchers at cybersecurity companies Check Point and Otorio analyzing this campaign discovered that the hackers exposed the stolen credentials to the public internet.
In a…
Source link
